It’s great that you’re thinking about how to protect your devices and avoid being ripped off by scammers. This is exactly what they don’t want. And it’s never been more necessary to make things difficult for cybercriminals.
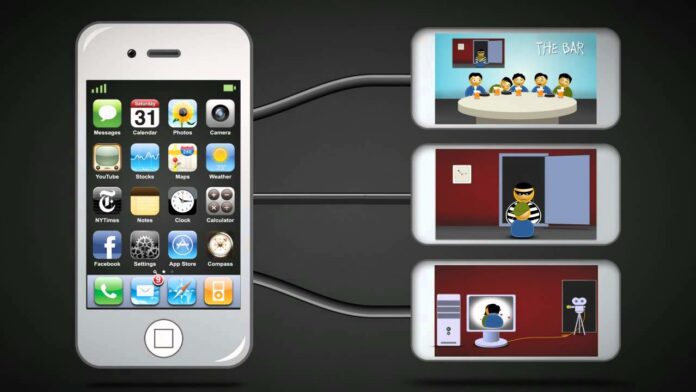
Game-changing technological advances include The Internet of Things (IoT), 5G connectivity, and Artificial Intelligence (AI). These are all exciting developments, but we’ve got to remember that criminals can use every one of these to access confidential data, steal identities, and spread malware, mayhem, and misinformation.
You don’t need to understand how your gadgets work to protect them. Making a habit of a few basic cybersecurity best practices can dramatically improve your online safety. And this will help secure everyone connected to you digitally.
Here are the top things you can do today to protect your gadgets and avoid scams. We’ll start with the major one and then throw in seven more to keep you safer and more secure.
1. Be Aware of Spam, Phishing, and Scamming Trends
Awareness is the number one way to protect yourself. Spam refers to communications that are sent indiscriminately — mostly by email — to large numbers of people in the hope that they will act on the contents. They are often sent by unprofessional marketing teams. And this approach is also often used by scammers who just need to trick a small percentage of recipients for their efforts to be worthwhile.
You can spot spam and phishing attempts — attempts to gain information with which to commit fraud, including identity theft — because they are likely to get your name wrong if they include it at all. And they tend to use dramatic words to make recipients feel special, such as telling them that they have been individually selected or that they’ve won a prize.
Scammers often rely on a classic combination of fear and urgency to get responses. They try to make people feel they will lose out on the offer if they do not respond immediately. Worse, they may suggest that there is a fine to pay or that the recipient must contact the IRS or another institution immediately to rectify an error.
Just remember fear and urgency. If the email has these hallmarks, treat it with extreme caution. You can check the authenticity of the email by:
- Looking for the sender address — if they claim to be the IRS but use Hotmail or Gmail, this is a big red flag.
- Look out for horrendous spelling and grammar. Spam emails tend to be very badly written. If you’re not good with spelling and grammar, ask someone you trust to check the email out. But don’t forward it.
- Hover over but don’t click on any hyperlinks — hovering offers users a preview of the hyperlinked URL. If it’s a shortened, hidden address, such as a TinyURL, be very cautious.
- Know that professional companies do not ask for user names and passwords or financial details via email or social media.
- If you have access to an unknown phone number and you’re suspicious about the sender, use PhoneHistory to verify its authenticity. With a massive database of US citizens, a reverse phone lookup here will give you the name and address of the owner, the carrier they use, and other interesting information, including how long they’ve been using that number.
If you identify spam or a scammer, block the sender and report the message as spam. Most email services provide this functionality as a matter of course, and the information they receive from you helps protect other people from harassment and manipulation by scammers. If in doubt, don’t click on any links, and do not reply. You can delete the email and back away slowly.
2. Be Aware of Personally Identifiable Information (PII)
In addition to being aware of spam and how scammers communicate, stay aware of PII, which includes data that could be used to identify you, such as your name, address, age, gender, phone numbers, and account details.
Be wary of anyone asking for PII. And if you’re filling in a form asking for PII, make sure it’s authentic. Look out for the padlock in the URL bar, which affirms that the site is using a secure, encrypted connection, and look out for other signs that the website is professional and authentic, similar to how you would assess an email that is potentially spam.
3. Perform Software Updates
When your device tells you it has found an update, don’t ignore it indefinitely. Most updates are related to security.
When software developers discover that hackers can get into their applications, they fix the issues and help everyone do the same via updates. Run and install them to keep your devices and their software as up-to-date as possible.
4. Avoid Unsecured Public Wifi
If you’re using unsecured wifi (such as the networks you find in airports and coffee shops, or your own if you don’t set the password), don’t. You can assume that everyone can see your online activity. While that might not seem very exciting to you, hackers are likely to make the most of opportunities to get into people’s devices and steal personal data, including financial information and personal details with which to commit better phishing attacks.
5. Install Antimalware
Understand that your attack surface — how hackers can access a network and files — extends to all your devices. Don’t leave a weak link. Install antimalware software on all your devices. Antimalware, such as McAfee Total Protection, will check your files and give you a heads-up if it spots suspicious activity or malware.
6. Read Privacy Policies
Agreed; this is not the most exciting way to pass an afternoon, but accepting terrible privacy policies is one of the ways that people become inundated with spam and harmful messages. Cast your eye over privacy policies to make sure they are not asking for permission to sell or reuse your data.
Reading privacy policies is especially important for sites where you might be asked for personally identifiable information, such as during an account creation process or making a purchase. If you’re entering your name, address, date of birth, and other identifying details, you want to be reassured by the company’s privacy policy.
7. Use Strong Passwords
Generally speaking, a strong password is at least 8 characters long and uses at least one capitalization, one number, and one symbol. These elements make it difficult for hackers and cybercriminals to guess your password. Even if they use bots and AI to do the cracking work — they do — it can still take many years.
Use PasswordMonster to check the crackability of your current passwords. Then go change them if necessary. Additionally, use different passwords for any sites where you have given financial data, such as credit card details. These, along with Google accounts, which tend to be tied to many other accounts — are the most important to protect.
8. Use Multi-Factor Authentication
Take security further by turning on multi-factor authentication. This is where you are prompted for at least two means of authentication, such as a one-time PIN code, a security question, or a biometric scan. Doing so doesn’t make your devices unbreakable, but it will put off a vast number of cybercriminals who will move on in search of a weaker target.
Conclusion
These are all practical tips that you can try today. Each one will improve the security of your gadgets and everyone connected to you online. Go ahead and share these tips if you find them useful because with the world becoming ever more connected online, we all need to work together to improve online safety (and give cybercriminals a bad day at the office).